Simple Setup
After deploying AlertD with the default CreateMonitoringRole setting (true), the IAM monitoring role was automatically created by CloudFormation. You only need to authenticate your team to start using AlertD.
Estimated time: 5-10 minutes
This guide is for deployments where AlertD monitors the same AWS account it is deployed in. If you need AlertD to monitor a different AWS account, follow the Advanced Setup instead.
Phase 1: Authentication Setup
Step 1: Access the AlertD Application
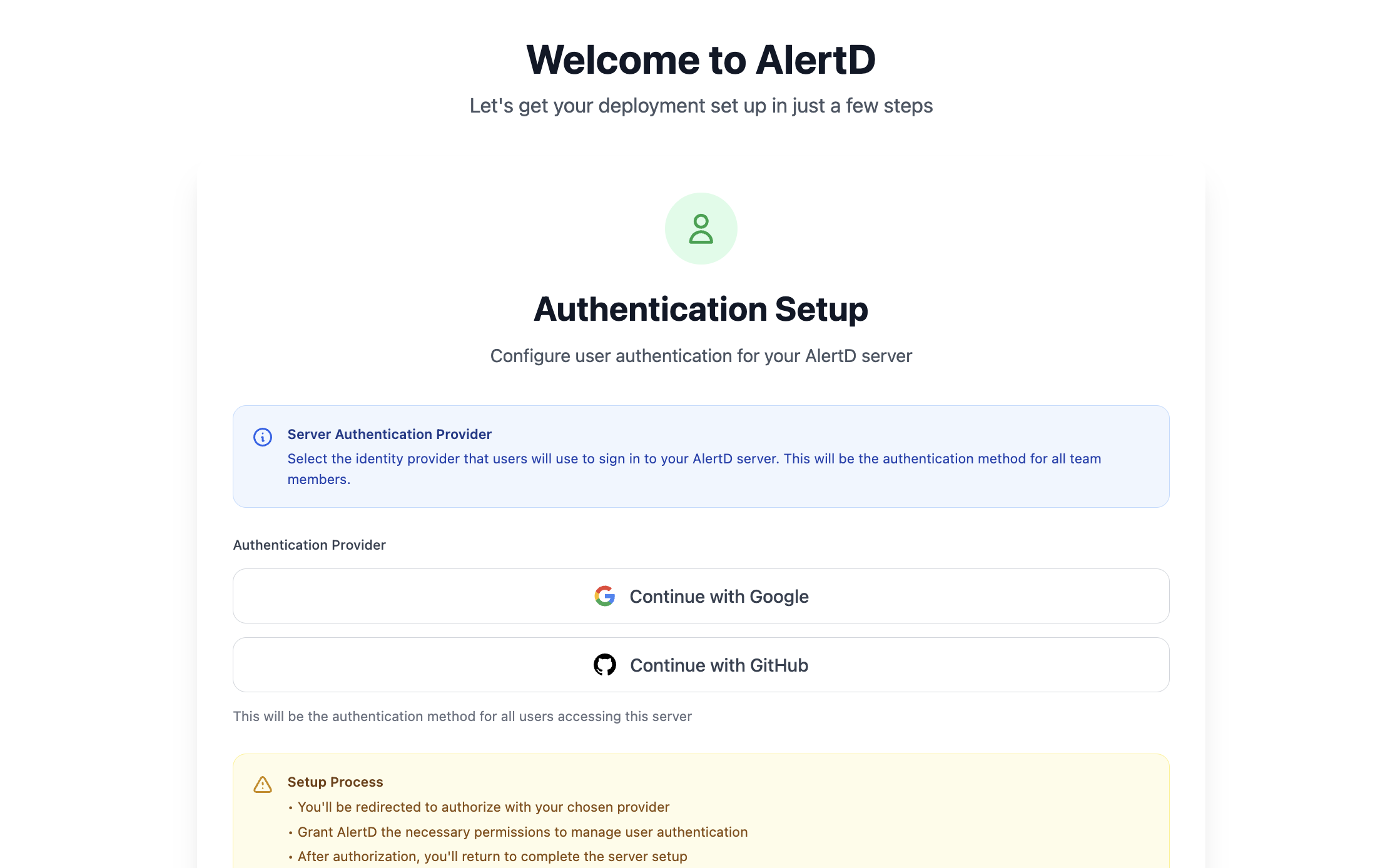
- Open the AlertDApplicationURL from your CloudFormation stack outputs
- Format:
https://AlertD-S-Alb-xxxx.us-west-1.elb.amazonaws.com - Or your custom domain if you configured DNS mapping
- Format:
- You’ll see the AlertD welcome screen with authentication options
Step 2: Choose Authentication Provider
AlertD supports two authentication methods:
- Continue with Google – Authenticate using your Google account
- Continue with GitHub – Authenticate using your GitHub account
Click your preferred authentication method to proceed.
Security Note: AlertD does not store your credentials. Authentication is handled entirely by Google OAuth or GitHub OAuth.
Step 3: Complete OAuth Flow
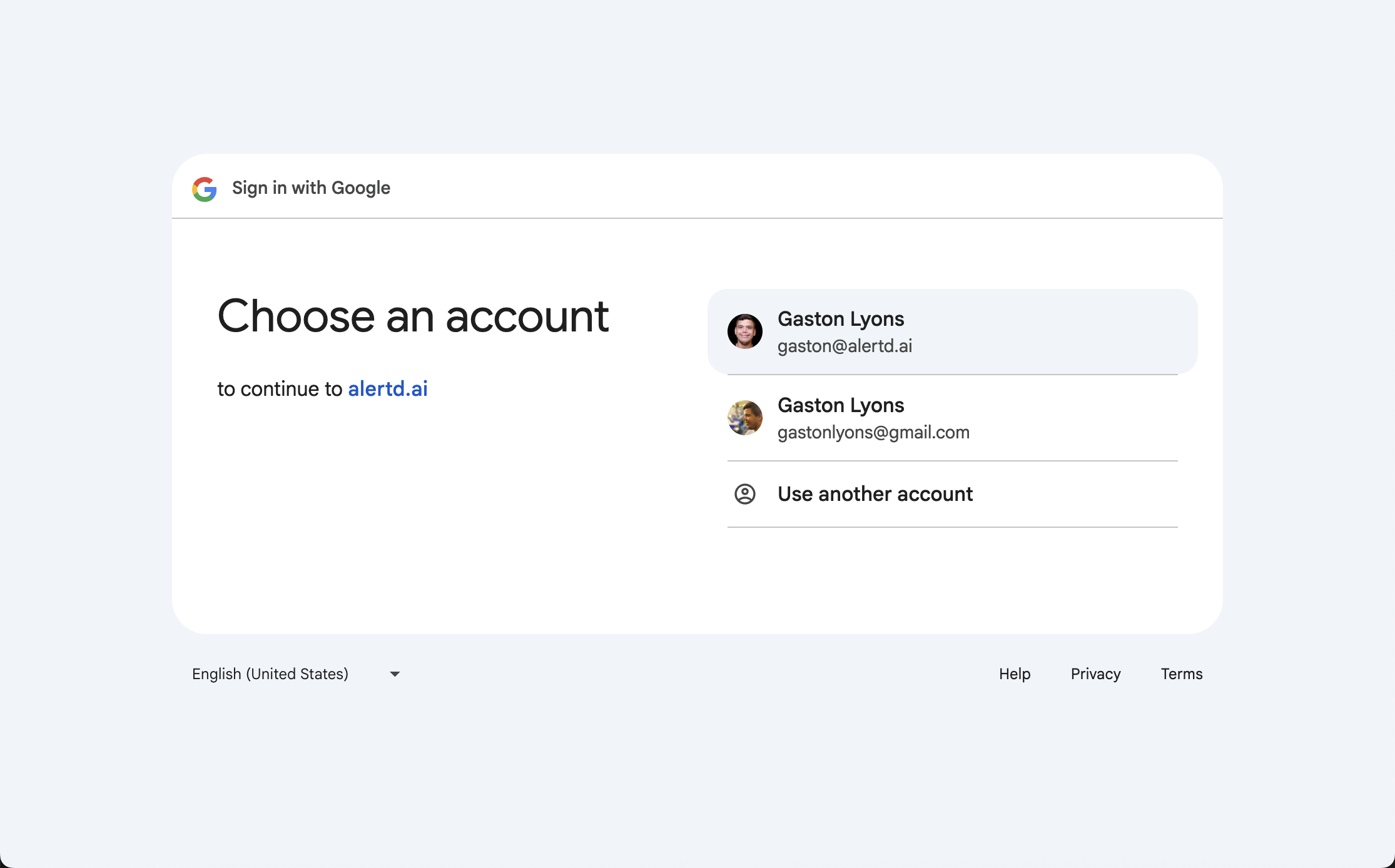
- A popup window will open showing your Google or GitHub login
- For Google:
- Select the account you want to use for AlertD
- Click “Continue” to authorize
- For GitHub:
- Authorize the AlertD application
- Grant necessary permissions
- You’ll be redirected back to AlertD once authentication is complete
Step 4: Verify Workspace Configuration
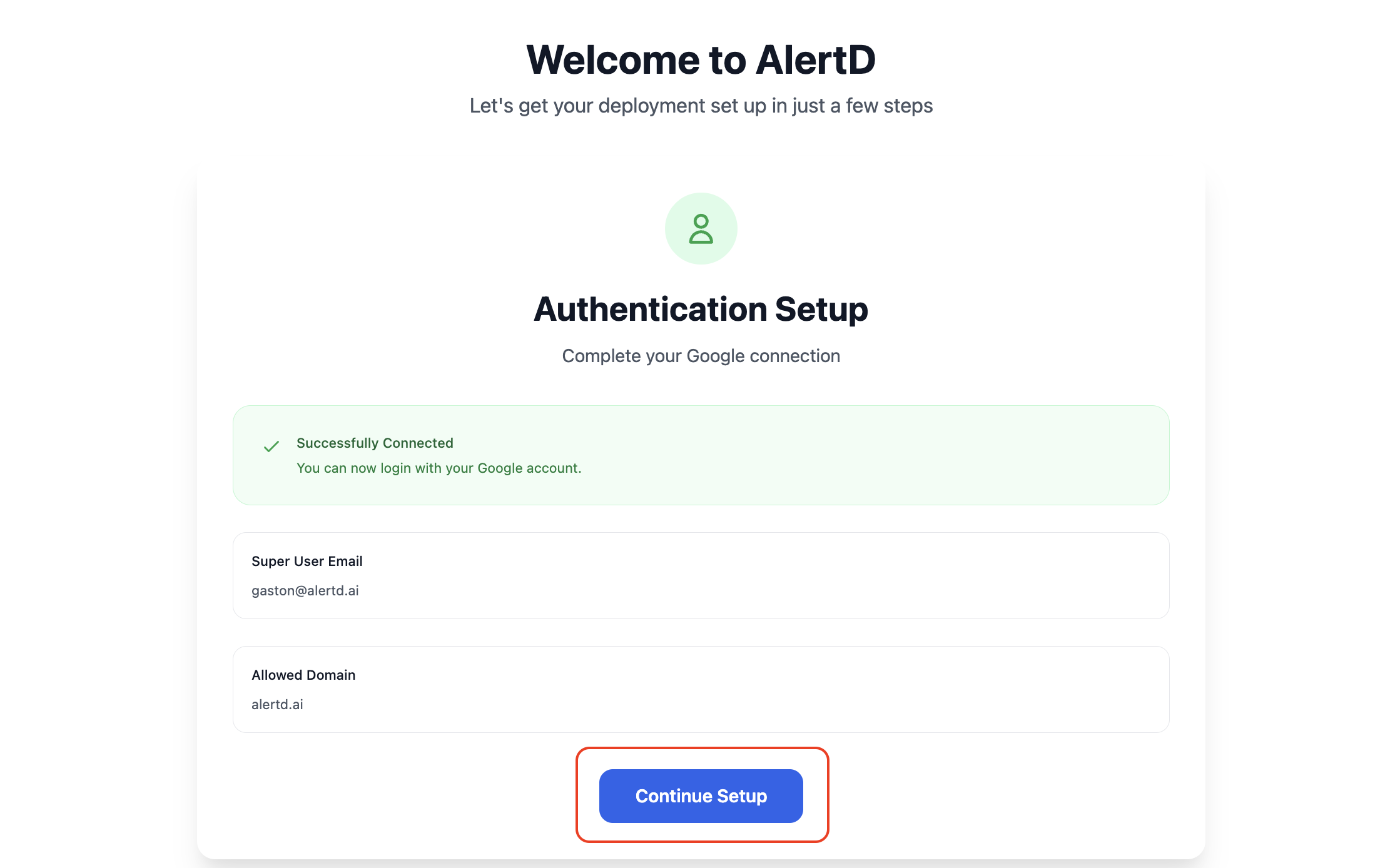
After successful authentication:
- AlertD displays a confirmation screen showing:
- Successfully Connected – Green checkmark confirming your OAuth connection
- Super User Email – Your authenticated email address (e.g.,
gaston@alertd.ai) - Allowed Domain – The domain associated with your workspace (e.g.,
alertd.ai)
- Your identity is automatically linked to a team workspace
- All users with the same email domain will share this workspace
- Workspace boundaries are enforced at the session and data layer
Click Continue Setup to proceed.
Phase 2: Access the AlertD Dashboard
Since you deployed with CreateMonitoringRole set to true, the IAM monitoring role was automatically created and configured. AlertD already knows the role ARN — no manual IAM steps are required.
Step 5: Access the AlertD Dashboard
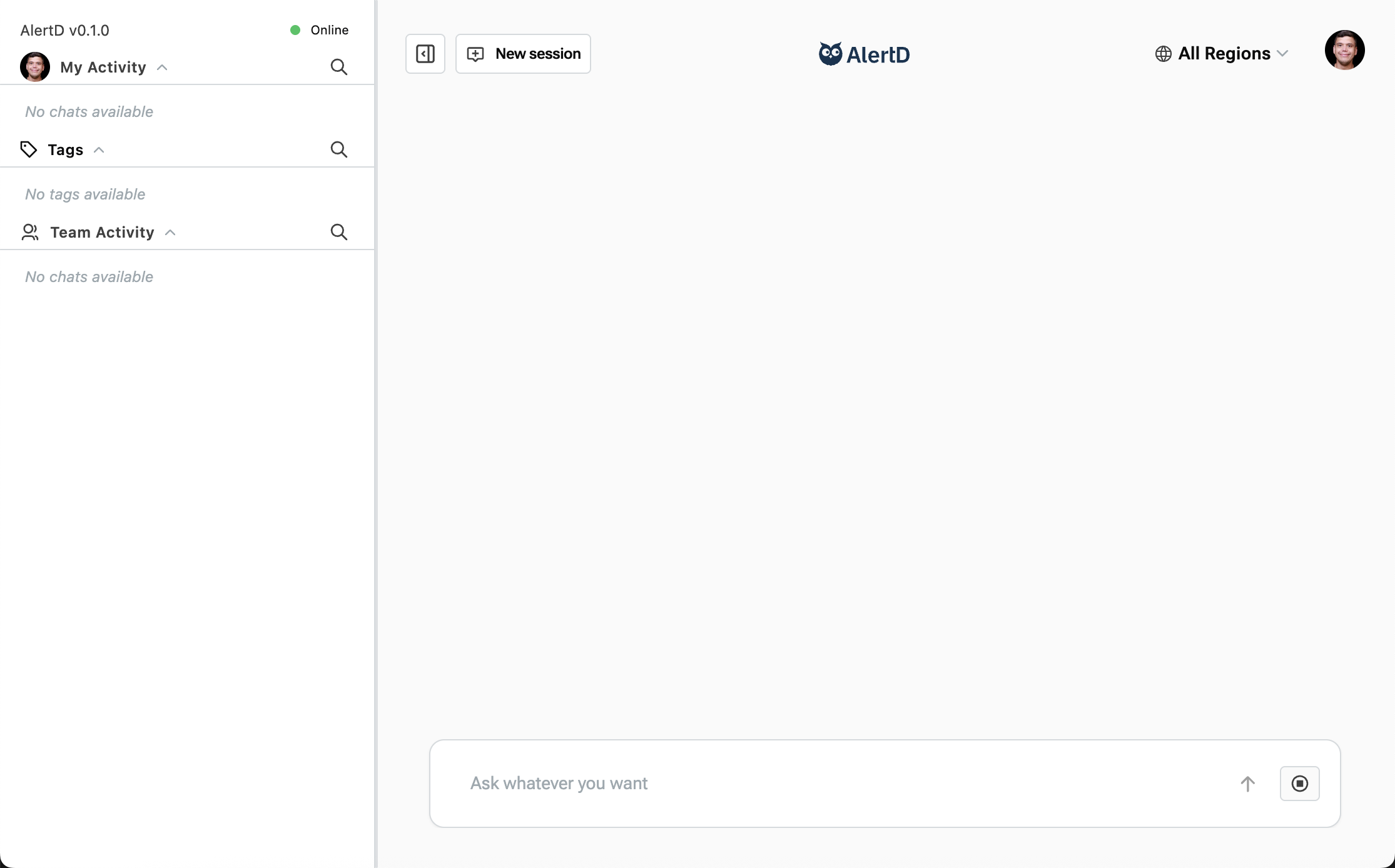
Once setup completes, you’re automatically redirected to the AlertD workspace:
Sidebar sections:
- My Activity – Your personal chat sessions and queries
- Tags – Organizational tags for sessions
- Team Activity – Shared sessions from your workspace teammates
Main workspace:
- New session button – Start asking questions
- Region selector – Choose AWS region (defaults to “All Regions”)
- Search bar – “Ask whatever you want” prompt
You’re now ready to ask your first question!
Setup Complete!
Your AlertD deployment is fully configured and ready to use. You now have:
- Authenticated workspace with team access
- Auto-created IAM role with read-only permissions to CloudWatch
- Access to the AlertD web interface
Troubleshooting
Authentication Issues
Problem: Cannot authenticate with Google or GitHub
Solutions:
- Ensure popup blockers are disabled
- Try a different browser
- Check that auth.demo.alertd.ai is accessible from your network
- Clear browser cache and cookies
Problem: After logging into Google/Github, you reach the following screen error:
Solutions:
- This is a known bug. Return to the previous screen and reauthenticate. We are actively working to fix this issue.
Connection Issues
Problem: Setup completion hangs or times out
Solutions:
- Verify ECS tasks are running in your CloudFormation stack
- Check security group rules allow traffic between ALB and ECS tasks
- Ensure private subnets have NAT Gateway for outbound internet access
- Review CloudWatch logs for the AlertD ECS tasks